No contracts. No commitments. No fees. Just the freedom to explore the features and functionality of the industry’s most comprehensive Zero Trust Network Access solution. Start now to test the power of direct-routed Appgate SDP built for complex hybrid infrastructures.
What You Get
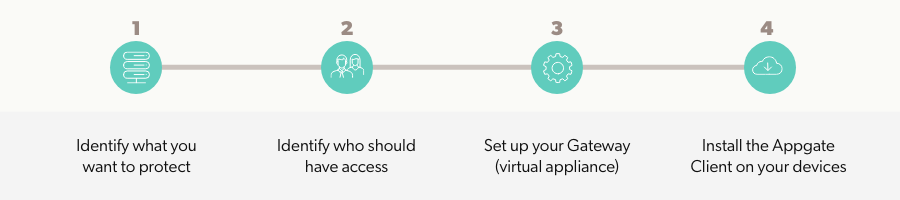
- Quick-Start Wizard: Be up and running in under an hour.
- Secure an unlimited number of applications: Set up secure access to as many applications, services and resources as desired.
- Unlimited dynamic policies: The wizard automatically configures examples to use or modify; you also can define an unlimited number of custom access policies.
- Online documentation: The admin guide covers key concepts like common use cases and technical details. The user guide details how to load the Appgate SDP Client to devices to enable secure access to authorized resources.
- On-demand demo library: Get direct access to our Zero Trust Demo Hub.
- Email support: Our experts will be on-hand to answer any questions.
Just 4 Easy Steps to Set Up Your Trial Environment